We are coming into intense times now in both fear mongering and in real dangers we must stay on top of, and now it becomes critical to discern which is which. Remember their objective right now, is getting our guns. They cannot proceed without them. That is why we must stay up during this critical time. Thank you and God Bless you for all you have done to support our efforts on all of our behalf.
Vatic Note: Clever. I wondered how these Khazar bankers were going to get around their loss of control of the information dominance they once had through their owned MSM. It appears they have wandered over to the alternative Internet press and found a sophisticated way to discredit bloggers, and commenters on alternative sites. They have to have agents working sites here that they bought up or hired to take the place of the MSM and thus make the alternative press work for them with or without knowing it.
Then they publish this showing that their agents are really good guys and to leave them alone. Its a counter balance to any discovery we may make on who the bad guys are and to be careful of them. We all have noticed a major increase in fear and hate based news stories and many of us have decided to either not publish them or to publish them and question the obvious gaps that do not make any sense.
This below is one of the ways to do it without anyone knowing its the khazar bankers after all and then harming the credibility of the blogger or saving the exposure of their paid blogger that they control, in either case, it affects truth telling and exposure.
I can always tell when a troll arrives because he criticizes the information we put up but does not provide any links or evidence that what we put up was wrong or false. I always ask nicely for him/her to do so and if the source is valid and credible, then I promise to post or publish it.
They NEVER respond with a link, rather name calling or insults. That is when I know we have a full fledge troll in the house. By the same token, I have been banned from sites where I either comment on gaps that need answering or information that is not validated or verified. Then I know the site that was a good one , is now in the hands of the PTB.
I knew the British were in on it, but I also noticed that the photo of the satellite dishes were done by Reuters, so that pulled a trigger for me, since Reuters is owned by Rothschild. What is going on here? I also noticed in this article a distinct lack of commentary about Israel. They listed all the other names of countries, but not the international bankers who are loyal to no nation, only to their class.
No mention of Rothschild, international bankers, or Israel. To me that is a major gap in this story that I would want addressed. Remember, NSA has a facility in Israel, and they have been fed spying info on Americans by the NSA. So why no mention of Israel or Rothschild? Read it and you decide. Remember all disinfo and propoganda has a smiggen or more of truth in it to give it credibility and that is what makes it hard to discern. It takes an enormous amount of experience to see it almost immediately. Keep practicing and we will prevail. Ferret out the truth parts and discard the rest.
RT: Western spy agencies build ‘cyber magicians’ to manipulate online discourse
http://jhaines6.wordpress.com/2014/02/24/rt-western-spy-agencies-build-cyber-magicians-to-manipulate-online-discourse/
by Jean, JHaines
Posted on February 24, 2014
 Satellite dishes are seen at GCHQ’s outpost at Bude, close to where trans-Atlantic fibre-optic cables come ashore in Cornwall, southwest England (Reuters/Kieran Doherty)
Satellite dishes are seen at GCHQ’s outpost at Bude, close to where trans-Atlantic fibre-optic cables come ashore in Cornwall, southwest England (Reuters/Kieran Doherty)Secret units within the ‘Five Eyes” global spying network engage in covert online operations that aim to invade, deceive, and control online communities and individuals through the spread of false information and use of ingenious social-science tactics.
Such teams of highly trained professionals have several main objectives, such as “to inject all sorts of false material onto the internet” and “to use social sciences and other techniques to manipulate online discourse and activism to generate outcomes it considers desirable,” The Intercept’s Glenn Greenwald reported based on intelligence documents leaked by former NSA contractor Edward Snowden.
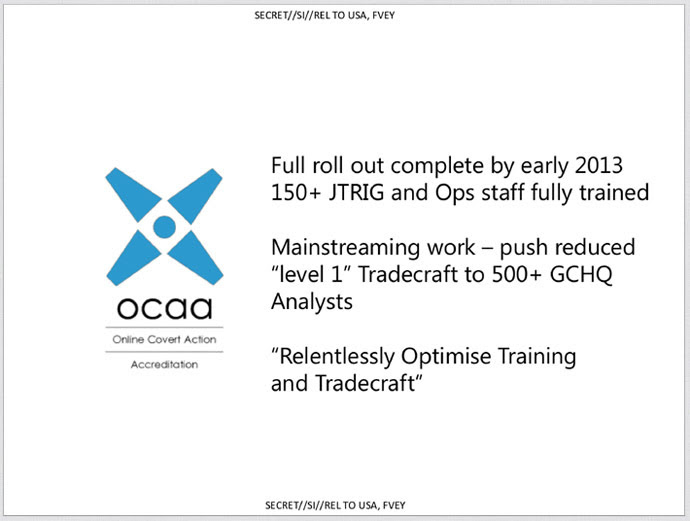
The new information comes via a document from the Joint Threat Research Intelligence Group (JTRIG) of Britain’s Government Communications Headquarters (GCHQ), entitled ‘The Art of Deception: Training for Online Covert Operations,’ which is top secret and only for dissemination within the Five Eyes intelligence partnership that includes Britain, the US, Australia, Canada, and New Zealand. (VN: here is where they neglected to mention international bankers, Rothschild or Israel, and especially Israel since they have total and complete access to NSA spying information which is supposedly top secret classified. So when did we give top secret classification to foreign countries or international bankers? Further, this then negates the value of the states that cut off utilities for NSA spying since they now have one in Israel and do not have to share our info.... they get it directly and then they decide whether to share it or not with NSA. Hmmm, a gap if I do say so myself. )
 Image from firstlook.org
Image from firstlook.org
The document outlines what tactics are used to achieve JTRIG’s main objectives. Among those tactics that seek to“discredit a target” include “false flag operations” (posting material online that is falsely attributed to a target), fake victim blog posts (writing as a victim of a target to disseminate false information), and posting “negative information”wherever pertinent online.
Other discrediting tactics used against individuals include setting a “honey-trap“ (using sex to lure targets into compromising situations), changing a target’s photo on a social media site, and emailing or texting “colleagues, neighbours, friends etc.”
To “discredit a company,” GCHQ may “leak confidential information to companies/the press via blog…post negative information on appropriate forums [or] stop deals/ruin business relationships.”
JTRIG’s ultimate purpose, as defined by GCHQ in the document, is to use “online techniques to make something happen in the real world or cyber world.” These online covert actions follow the “4 D’s: deny, disrupt, degrade, deceive."
 Image from firstlook.org
Image from firstlook.org
As Greenwald pointed out, the tactics employed by JTRIG are not used for spying on other nations, militaries, or intelligence services, but for “traditional law enforcement” against those merely suspected of crimes. These targets can include members of Anonymous, “hacktivists,” or really any person or entity GCHQ deems worthy of antagonizing.
“[I]t is not difficult to see how dangerous it is to have secret government agencies being able to target any individuals they want – who have never been charged with, let alone convicted of, any crimes – with these sorts of online, deception-based tactics of reputation destruction and disruption,” Greenwald wrote.
In addition, the targets do not need to have ties to terror activity or pose any national security threat. More likely, targets seem to fall closer to political activists that may have, for instance, used “denial of service” tactics, popular with Anonymous and hacktivists, which usually do only a limited amount of damage to a target.
 Image from firstlook.org
Image from firstlook.org
“These surveillance agencies have vested themselves with the power to deliberately ruin people’s reputations and disrupt their online political activity even though they’ve been charged with no crimes, and even though their actions have no conceivable connection to terrorism or even national security threats,” Greenwald wrote.
In addition to the personal attacks on targets, JTRIG also involves the use of psychological and social-science tactics to steer online activism and discourse. The document details GCHQ’s “Human Science Operations Cell,” which focuses on “online human intelligence” and “strategic influence and disruption” that are used to dissect how targets can be manipulated using “leaders,” “trust,” “obedience,” and “compliance.”
Using tested manipulation tactics, JTRIG attempts to influence discourse and ultimately sow discord through deception.
When reached for comment by The Intercept, GCHQ avoided answering pointed questions on JTRIG while insisting its methods were legal.
“It is a longstanding policy that we do not comment on intelligence matters. Furthermore, all of GCHQ’s work is carried out in accordance with a strict legal and policy framework which ensures that our activities are authorized, necessary and proportionate, and that there is rigorous oversight, including from the Secretary of State, the Interception and Intelligence Services Commissioners and the Parliamentary Intelligence and Security Committee. All our operational processes rigorously support this position,” GCHQ stated.
Posted in Financial/economic information, Illuminati/
(End of article)
++++++++++++++++++++++++++++++
The second article is just as important to watch and absorb, because it lays out in a nutshell what the elite planners see in their long range goals to turn us all into cyber-humans.
Daniel has some very interesting thoughts about "TransHumanism". Creating hybrids and humanoids by the elite. The "Cloud" that is becoming increasingly popular, at the cost of eliminating privacy. GMO foods created to sterilize human populations. The elite are using their advanced technology to create the "Hive Mind" so that there cannot be any resistance to their power. Very interesting stuff indeed.
Daniel has some very interesting thoughts about "TransHumanism". Creating hybrids and humanoids by the elite. The "Cloud" that is becoming increasingly popular, at the cost of eliminating privacy. GMO foods created to sterilize human populations. The elite are using their advanced technology to create the "Hive Mind" so that there cannot be any resistance to their power. Very interesting stuff indeed.
The article is reproduced in accordance with Section 107 of title 17 of the Copyright Law of the United States relating to fair-use and is for the purposes of criticism, comment, news reporting, teaching, scholarship, and research.

1 comment:
Thank you for this insightful post, some blogs bombard us with posts predicting the Iraqi Dinar Reevaluation, others with docs we can't even understand let alone think of using, this blog however, gives an arrange of topics is hard not to always come back to it. Always interesting and informative your blog, in my opinion, is one of the best. Thank you for the time and effort.
Post a Comment